The first episode of our “Na vlne kodu” podcast (in English On the Wave of Code) was prepared in cooperation with the online platform Ksebe.sk. With Dominika Neprasova we talk about how to set boundaries between work and private life, how to avoid burnout or how to say no. We wish you a pleasant viewing, listening or reading.
In today’s episode, we’re going to cover a topic that is increasingly topical in our hectic society. It’s Healthy Work-Life Boundaries. While technology is great, it can make it difficult for us to rest and recover, resulting in overwork and, in extreme cases, burnout.
This theme resonates not only among the wider public, but also in various specific professions – for example, in the IT sector, where constant connectivity and technological pressure can cause problems with We’ll take a closer look at why work-life boundaries are so important and how to respect them. Our guest is psychologist Mgr. Dominika Neprašová from the online platform Ksebe.sk.
Podcast “Na Vlne Kodu”
‘Na Vlne Kodu’ (On the Wave of Code) is an IT podcast by msg life Slovakia. It regularly covers topics from the fields of psychology and HR, as well as IT news. Listen to more episodes of Na Vlne Kodu.
Dominika, thank you for coming. Tell us something about yourself. What made you start focusing on the boundaries between work and private life?
Thank you very much for the invitation. I am a psychologist at the Ksebe platform and also at the Salvus health centre in Bratislava. I am involved in counselling and therapy with young adults and adults, either individually or in a couples context. I am also enrolled in long-term psychotherapy training and in the specialty of clinical psychology, which is like the certification that doctors have in our country.
My psychological journey was first preceded by a career in HR. I worked in this field for four years. I started at the Grafton recruitment agency, then I worked in People Operations, or HR, at a Slovak start-up, where I was responsible for the overall care of employees.
And it was in this context, maybe because of my psychology background, that I started to pay more attention to the topic of worklife balance. People are overworked, they often tend to burn out. They don’t know how to set boundaries, they don’t know how to use the word NO.
These themes also come up in my psychology practice. While for young people the most common themes are relationships, emotionality or self-development, the older or middle generation mainly deals with the topic – how to set up a work-life balance and what themes emerge in it. Everyone has their own themes in their career, such as self-worth, self-fulfilment, self-esteem, etc. And in that whole context, those themes actually intertwined into my current work.
What is the definition of healthy boundaries?
Healthy boundaries define our living space: not only the physical, but also the mental, which is subjective. Having boundaries means keeping your distance from other people, knowing how to say no, stand up for yourself and take care of yourself. This protects us in a dynamic world where we can sometimes be shouted down by the louder ones. Healthy boundaries serve to define us in a certain way, and that can ultimately help us.
‘Healthy boundaries define our living space. They give us the opportunity to express who we are, to say no, and to stand up for ourselves.’
In today’s world, we are often faced with the need to be online all the time. Technology forces us to work harder than is healthy. How does this affect our mental and physical health and our lives? How to prevent burnout?
This is quite difficult to observe. If we don’t have the capacity for self-reflection and self-awareness, sometimes we have trouble stopping. Time is really fast and the stimuli are many.
I often ask my clients what they would find out about themselves if the world stopped now. Sometimes I get answers like – maybe I’d find out I’m overworked. Well, and those boundaries at work manifest themselves, for example, in the way that we can’t keep deadlines, we do overtime because we have to, because the work won’t wait for us. We can’t say no to colleagues, we’ll get involved in 35 projects even though we know it’s beyond our limits.
“Ask yourself: What would you discover about yourself if the world stopped right now?’
Mentally it affects us in that we are tired, overworked, exhausted. It affects our mood a lot. We are often explosive, reacting to every little stimulus. Hand in hand with this go the physiological aspects. A lot of us get sick because when we are under prolonged stress and expectations, immunity breaks down.
For example, one of my clients was always sick. And then we found out that she was actually still stressed. But physiology doesn’t have to be just about immunity, it’s also associated with migraines or headaches, for example. It can also be related to the fact that we sit a lot at work and our musculoskeletal system suffers. Everything is very interconnected and for someone problems appear in both areas, for someone only in mood changes, for example. Psychosomatics are also very common, for example various digestive, stomach problems. The body reacts to stress, and digestive problems are currently at the top of the list of symptoms by which people react to stress in their lives.

Read also: Back pain from sitting at a computer: Tips for correct posture and workout.
How does this affect our overall productivity and happiness?
We psychologists are told to take care of ourselves first and then take care of others. This is actually said on the flights as well. We always have to put the mask on ourselves first and then the child. And that is really true. Because if we don’t have energy, we can’t do anything for other people. It impacts our happiness, how we approach our work, how we handle stress and respond to stimuli. It applies also to me, my clients can sense if I’m tired. We just can’t fake our body language.
‘Take care of yourself first. Only then will you be able to take care of others.’
What are the long-term consequences of not having free time, of not being able to make time for ourselves?
We are suppressing ourselves. Each of us needs fulfillment in more areas than just work. We have three roles in our lives. They are work, family and social relationships. If we don’t think of our limits and suppress them, the overwork, the lack of energy, the fatigue, the illness, the exhaustion, the mental collapse to burnout – these are all consequences that are evidently clear, not only in the waiting rooms of doctors when people want PN’s, but also in us psychologists.
People just can’t take it anymore. They don’t like doing the work as much as they used to, and the fire is going out of them. If one is capable of empathy or sensitivity, one sees in people how they change.
Why do you think it’s hard to set boundaries?
FOMO (Fear of Missing Out) syndrome is very common in Generation Z or the younger generation. They don’t want to miss anything, they want to be everywhere, they want to be involved in everything so they don’t miss out. And it spills over into the work sphere as well. When they have the opportunity to work on such a project, to go on such a service and to help in this, they want to realize themselves in every way.
At the same time, there may be mental aspects to it, such as feelings of inadequacy or imperfection. People who can’t set boundaries are often perfectionists, and they have a lot of other issues that get in the way of them setting boundaries. Everyone has their own beliefs in setting boundaries and some private logic that they work from. That is, if I have a private logic that if I don’t do my best, I won’t be good enough, then I’m going to do 120% so that my beliefs don’t come true.
What does burnout syndrome look like in the general public? Is it different for people who work in IT, for example?
On first hearing, I would say there is not that much difference. Burnout syndrome or burn-out syndrome has 4 phases. First we react to stimuli with great enthusiasm, then the enthusiasm gradually decreases, frustration, mood swings, a drop in energy, until it hits the nervous system and the body to the point where we actually drop completely. A lot of people also end up in intensive care or in bed because the body collapses.
Well, although at first glance there’s probably not that much difference, when we focus more on the IT area, it’s really very specific. IT people have very sedentary jobs that are often monotonous and extremely focused. Burnout in them can result just from the fact that they’re spending, say, 12 hours a week paying attention to something very intense.
At the same time, IT professionals are often more introverted. That’s not a stereotype, it’s really about the fact that they choose to work that way because of it. Just the fact that they are not in touch with the outside world, but only with themselves, their head and the job, can lead to burnout.

Our tip: In our next podcast, we’ll take a closer look at the topic of Burnout.
Let’s take a look at individual strategies to improve your work/life balance. What are the experts’ recommendations and your personal tips on how to improve our work/life balance?
Working in HR, but also psychology, has taught me that when results speak, those are the ones that speak the loudest. It’s just the best argument we have. Someone is really capable of getting the job done in 6 hours, and for 2 hours they can just spin around in a chair. Someone takes longer, everyone has their capacity.
For example, I am a person who loves my free time. This is also due to the fact that I don’t have a family, I don’t have children, so I have more free time and it doesn’t quite compare. But I’m so burdened by it that I feel it on myself when I don’t have enough of it. When I had a lot of projects when I was a student, I felt like I wasn’t enjoying it at all. All I had in my head was that I had to be there and I had to do it. It was so overwhelming that I said enough is enough and made a change. I made it quite early, I was 25 at the time. For somebody, it comes later when the burden hits them.
It helps a lot to make to-do lists, for example. Plan what I am able to do for the day. It helps someone to realistically check off tasks so they can see them and have tangible proof of what they planned and what they accomplished.
And at the same time, if tasks happen to keep me at work longer, it’s only natural. I’ll drag it out longer, but then I think to myself, and if there’s an opportunity, I’ll leave early the next day. For example, when I had interviews at work until six to seven, which was long after my work hours were over, I would then leave a little bit early that next day. Because the working hours are 8.5 hours, unless somebody has set it otherwise. It is standard working hours.
Plus we have some KPIs or some indicators of the results of our work. If I meet those KPIs, I don’t have to meet them 100%, but at least 85%, the work still has to wait for the next day. So why not take that time for yourself? Why not leave work at that seventeenth hour and spend time with family or your hobbies, or just sit down and relax on the couch?
The theme of toxic hyperactivity or productivity also lives in society. We still have to do something. But we don’t have to. We are overloaded. Even after work, we’re still in a rut. We don’t have to function that way. It’s perfectly fine to sit down, relax, watch a show or go for a walk. That’s also an active pastime. So the most important tips are that we need to think about ourselves because it’s going to catch up with me somewhere anyway, at the same time that work will always have tasks waiting for us and that if we can deliver those results, we have an ace up our sleeve.
How to organize our time better? How should employers support their employees in maintaining a good work-life balance?
It is important to remember that our life is a series of decisions. So it is our decision to set a healthy boundary or to have that work life balance. We decide whether we will still go do xy other activities after work or just relax. We have that fully consciously in our hands. When someone says they can’t, they’re making excuses. We can decide how we allocate that time.
The best indicator of how to set this up in companies is to lead by example. Whether we’re in the HR department or we’re in senior management, we’re team leaders, etc. I’ve worked with a number of managers who have really led by example for their employees. I also had a boss who knew that we were doing 100% during the work day, sometimes up to 120 and sometimes she would send us home at 4 o’clock. And she went home too. She was an example to us both in that she didn’t let herself get completely worn down by the work, and she also built up in us the awareness that work-life balance is very important.
If managers were able to set an example for employees, employees might view boundaries differently and the overall company culture would be affected. Because it is different to say that we have the corporate benefit of work-life balance, only then what is the reality? Is that really what the leaders of that company, or the corporate culture bearers, are doing? Or is it just a marketing ploy to attract employees?

Read also: Interview with a psychologist: Do companies have a responsibility for employee mental health?
What practical tools can we use to better manage our time? What would you recommend?
The most important and practical tool is to realize that I can decide how I am going to manage my time. At the same time, I have to realize what themes enter into it when I can’t have that work-life balance, for example. If someone tells me they can’t do that, we go over the themes together. Because not knowing how to have a work-life balance is actually purposeful behavior. It brings something to us that we can’t steady it, and that’s what I go after with those clients.
Practical tips include, for example, planning a program for myself to look forward to after work. That I’m going to put that spin on it, that I’m going to quit my job and I’m going to dedicate myself to this. Because if we can choose to be at work longer, we can choose to be at work a little bit shorter. Of course, with the limitations that work has.
Something different works for everyone, it’s hard to answer in general like that. I don’t really work that way anyway, because people can read tips on the internet on how to work with boundaries. But once we realize that it’s about those conscious decisions, one can change the rhetoric. That I don’t have to, but I can. Even that perception will affect how we think about it. When we change our thinking, it will affect how we behave and ultimately how we feel. It’s like a formula or a lineage of those steps that are interconnected and we can influence them nicely for ourselves.
“Change your mindset from ‘I must’ to ‘I can’. When you change the way you think, your behaviour and how you feel will change too.”
Do you think we use the word NO enough? What rituals can we cultivate to help us properly define healthy boundaries?
The word NO is extremely important, but we use it extremely little. In particular, our generation, and perhaps partly the previous generation, has not been led to say the word. I have many friends who already have children. If they are with their grandparents and they say NO to something, those grandparents will say she is an ugly little girl, NO is not said. This is exactly what we have coded into us. That’s why it’s extremely difficult for us because we don’t know how to use the word NO.
Saying NO is very important and in many situations even self-preserving. I don’t want to go to the extreme, but I can think of many different situations when saying NO is really necessary.
There’s a pretty good tip to start saying NO when it’s very sharp for us because we didn’t know how to use it before and suddenly we’re supposed to do it. When I want to communicate something, for example healthy boundaries, quite in the middle are the so-called “I” statements, through which I speak through myself.
I don’t have to say NO, I’m not going to do this. What I can say is that I’m totally uncomfortable doing this work because it causes me stress, puts me in a bad mood, or I know that I might be prone to failure and I’d rather avoid this work or get involved in some other project. It’s like such a roundabout way of saying this, but at the same time it’s not, because JA’s statements bring us back to ourselves and to the awareness of what we need, what we want and what we are experiencing.
‘We are not used to saying no. However, it is very important to do so. However, we can communicate healthy boundaries through ‘I’ statements.’
NO is really an extremely big topic. Even when clients come to me with other topics, we always get to that NO. This is because the inability to say NO is associated with other topics. Even in that work context, I can imagine it quite beautifully. I can’t say NO to my boss because she just needs a little help with something, even after hours. But I won’t say NO to her because she’s my boss. People are afraid of being replaceable. In a work context, we are also concerned about salary, about having a job. We have to support ourselves, a family, so it’s kind of that lash over us that just don’t say NO.
But I think if we say NO, people will respect us a little bit more. Because if we’re always nodding at somebody, people get used to it and they completely violate our personal space and respect goes down a little bit. If someone keeps saying yes to us, we get so used to it that then we’re totally waving to that person.
Can you share some specific examples from practice? Do you know people who have successfully managed to set work-life boundaries? How did they manage to do it?
A lot of times people get it when they come into therapy. Because they come when they feel that something is wrong, when they are dissatisfied, sad, nervous and so on. If we examine those areas of life that I was talking about, we come to the conclusion that the problem is somewhere at work, for example.
As an example from my practice, I have one client who needed to change jobs. She couldn’t set healthy boundaries in her original one. But not because she couldn’t, but because the culture and environment prevented her from doing so. Also, admitting to change and finding a new job is actually building that healthy boundary against a toxic work environment.
Another client, for example, had a huge self-evaluation in the topic of the thesis. When she didn’t do something 100%, she felt that she had completely failed, that she was inadequate, imperfect. She was able to build healthy boundaries by realizing that anyone can make a mistake at work. It doesn’t mean she is bad or imperfect. She was able to separate herself and her self-worth from her work, and that’s what helped her build that healthy boundary.
I also had a client in a management position where the topic of healthy boundaries was about how to find and build them outside of work. He didn’t set boundaries at work because he didn’t know what values to pursue after that job. We named what he would enjoy, what he would like to pursue and then he didn’t need to be at work for 15 hours because he knew he could go play golf afterwards, for example.
The examples are really different, but if I have to underline something, it is the fact that everyone has their own themes involved. For example, if we don’t know how to say NO, which makes it difficult to set healthy boundaries, it can also be the obedient child syndrome. That I don’t want to disappoint others, I don’t want to upset others’ expectations, I want to be liked, I want to be accepted. This particular theme is very common.
Dominika, if you had something else to recommend to our listeners – maybe just one piece of advice for maintaining those healthy boundaries, what would it be?
It may sound pathetic, but I would say there is only one life. If we sacrifice it just to work, we lose a lot of those nuances or other aspects of life that are waiting for us. Work always will be and always has been. Those emails and phone calls will just wait for us. At the same time, if we realize that if we don’t have those boundaries and if we don’t have the energy for ourselves, we can’t keep putting it out and we can’t put it into that work.
If we are to be productive at work, work-life balance and healthy boundaries can help us do just that, because the work itself will reflect that perfectly. Whether we have the capacity for it, whether we are nice to our colleagues or whether we argue with everybody, are irritable, it will show in that work. And so in other areas of life, in our relationship with ourselves and so on.
‘There’s only one life. Do you really want to sacrifice it for work?”
And what tools and resources would you recommend to support a better work-life balance? What about, for example, IT professionals who are feeling overwhelmed, overworked and looking for a way to find balance?
At work, it would definitely be frequent breaks for that physiology, for that movement, but also for that mental reboot. If they work from home, certainly some socialization. If the IT professional or the female professional has the capacity to do that, then contact with a community, with a human being, is really very necessary. Well, and just try to find some hobbies of their own, so that they’re not just behind a computer, for example.
Dear listeners, thank you for joining us today. We say goodbye to you Mgr. Dominika Neprašová and for msg life Slovakia Ivana Hricová. Remember, it is okay to set boundaries and take care of your health. Continue to follow us on social media such as Facebook, Instagram, LinkedIn and also our website msg-life.sk, where you can find out more about other episodes from the field of HR, psychology or news from the world of IT. Our next topic will be Working from home and its impact on well-being. Have a great day and don’t forget to relax and switch off.

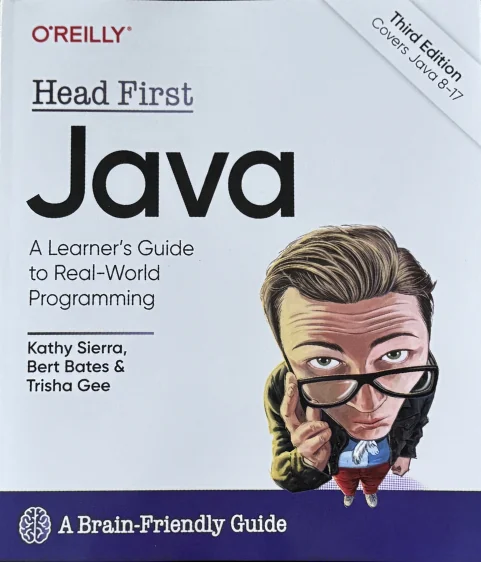 The Head First Java book builds gradually in the following chapters, on previously explained points, which means that the information is dispensed gradually. However, the book cannot simply be used as a reference guide.
In terms of content, the book begins with an introduction on how to use it effectively, and in the following chapters explains the features of the object-oriented Java language, covering objects and classes, primitive variables and references, object state and behavior, operators, loops, and even programming a game similar to boats.
He will then explain the JAVA API (libraries), moving on to more advanced concepts such as inheritance, polymorphism, and relationships between objects. Then comes object management, mathematical operations, sorting and data manipulation.
Advanced topics include data streams, serialization, Swing and JavaFX overviews, parallel processing. Finally, the book transparently mentions a list of Java features that didn’t make it into the book.
The code in the Head First Java book is well explained and helps in practicing the acquired Java knowledge.
Although the information in the book is correct, the dynamic developments of recent years have made many of the concepts obsolete and they are no longer used today. For example, I will mention Swing, which has been completely replaced by JavaFX technology and it is quite rare to encounter a GUI implemented on Swing technology today. Of course it is not a problem to skip these parts and continue reading.
The Head First Java book builds gradually in the following chapters, on previously explained points, which means that the information is dispensed gradually. However, the book cannot simply be used as a reference guide.
In terms of content, the book begins with an introduction on how to use it effectively, and in the following chapters explains the features of the object-oriented Java language, covering objects and classes, primitive variables and references, object state and behavior, operators, loops, and even programming a game similar to boats.
He will then explain the JAVA API (libraries), moving on to more advanced concepts such as inheritance, polymorphism, and relationships between objects. Then comes object management, mathematical operations, sorting and data manipulation.
Advanced topics include data streams, serialization, Swing and JavaFX overviews, parallel processing. Finally, the book transparently mentions a list of Java features that didn’t make it into the book.
The code in the Head First Java book is well explained and helps in practicing the acquired Java knowledge.
Although the information in the book is correct, the dynamic developments of recent years have made many of the concepts obsolete and they are no longer used today. For example, I will mention Swing, which has been completely replaced by JavaFX technology and it is quite rare to encounter a GUI implemented on Swing technology today. Of course it is not a problem to skip these parts and continue reading.